Hybrid Cryptography Model based on Authentication, Integrity & Privacy: Kapoor, Vivek, Bhat, Saurabh: 9786202010085: Amazon.com: Books
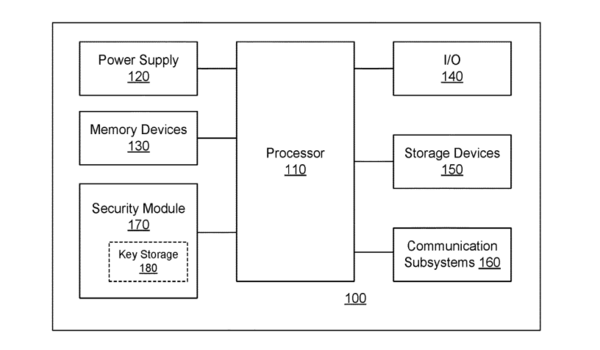
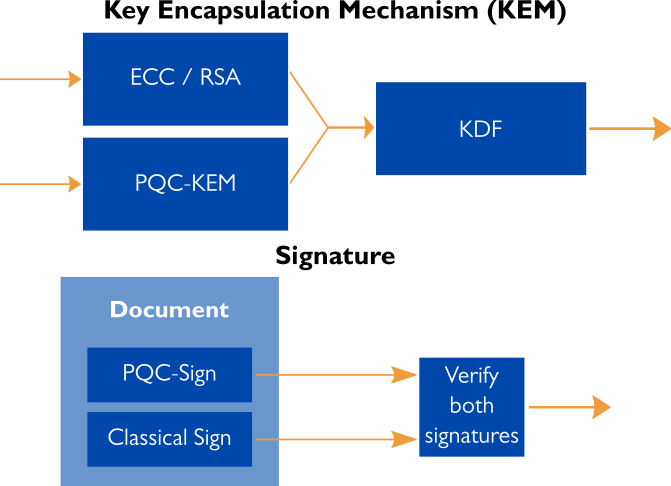
Quantum-augmentable hybrid encryption system and method - Ted Rogers School of Management - Toronto Metropolitan University

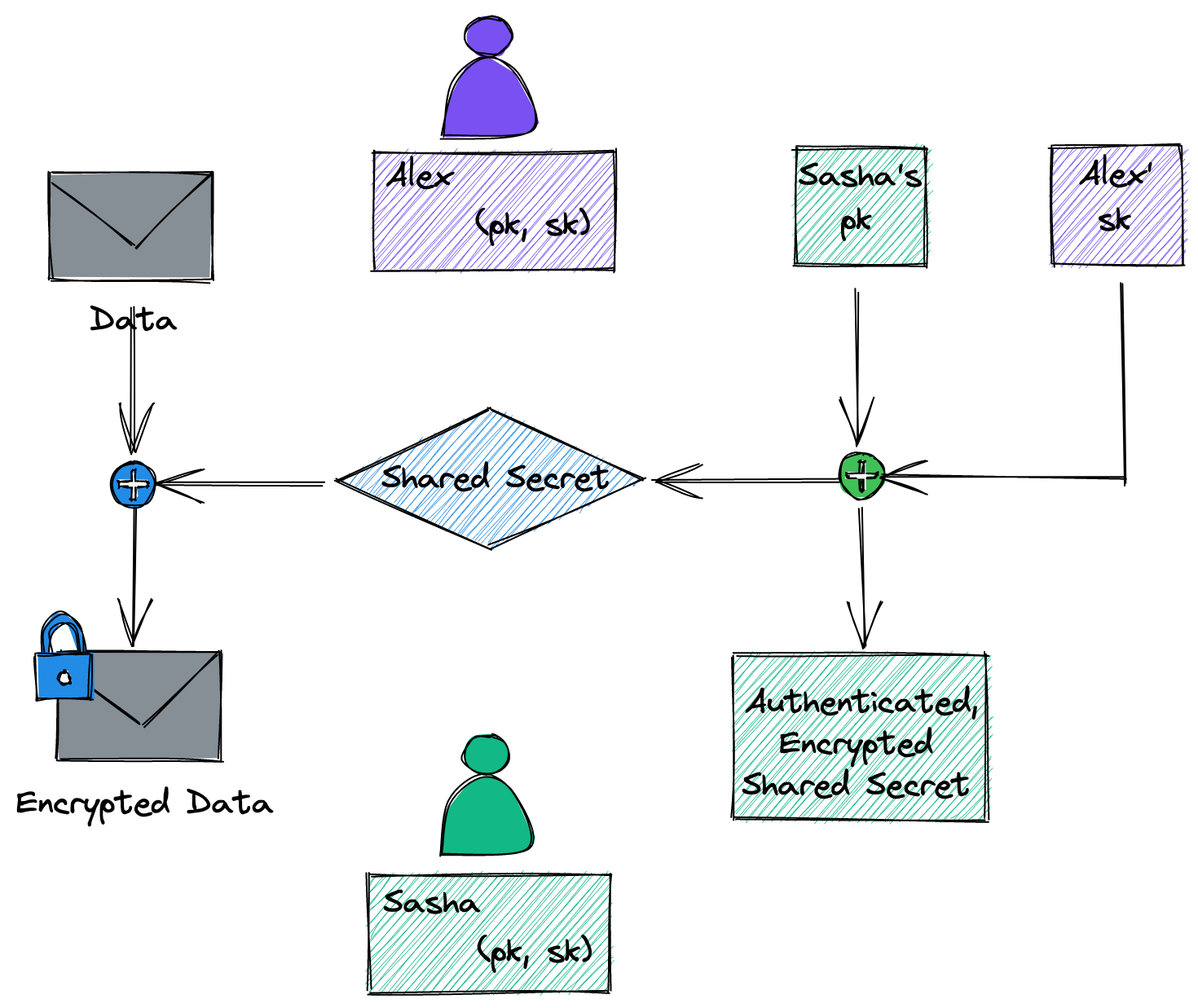
A Comparative Study of Various Traditional and Hybrid Cryptography Algorithm Models for Data Security | SpringerLink

A Novel Hybrid Encryption Method to Secure Healthcare Data in IoT-enabled Healthcare Infrastructure - ScienceDirect
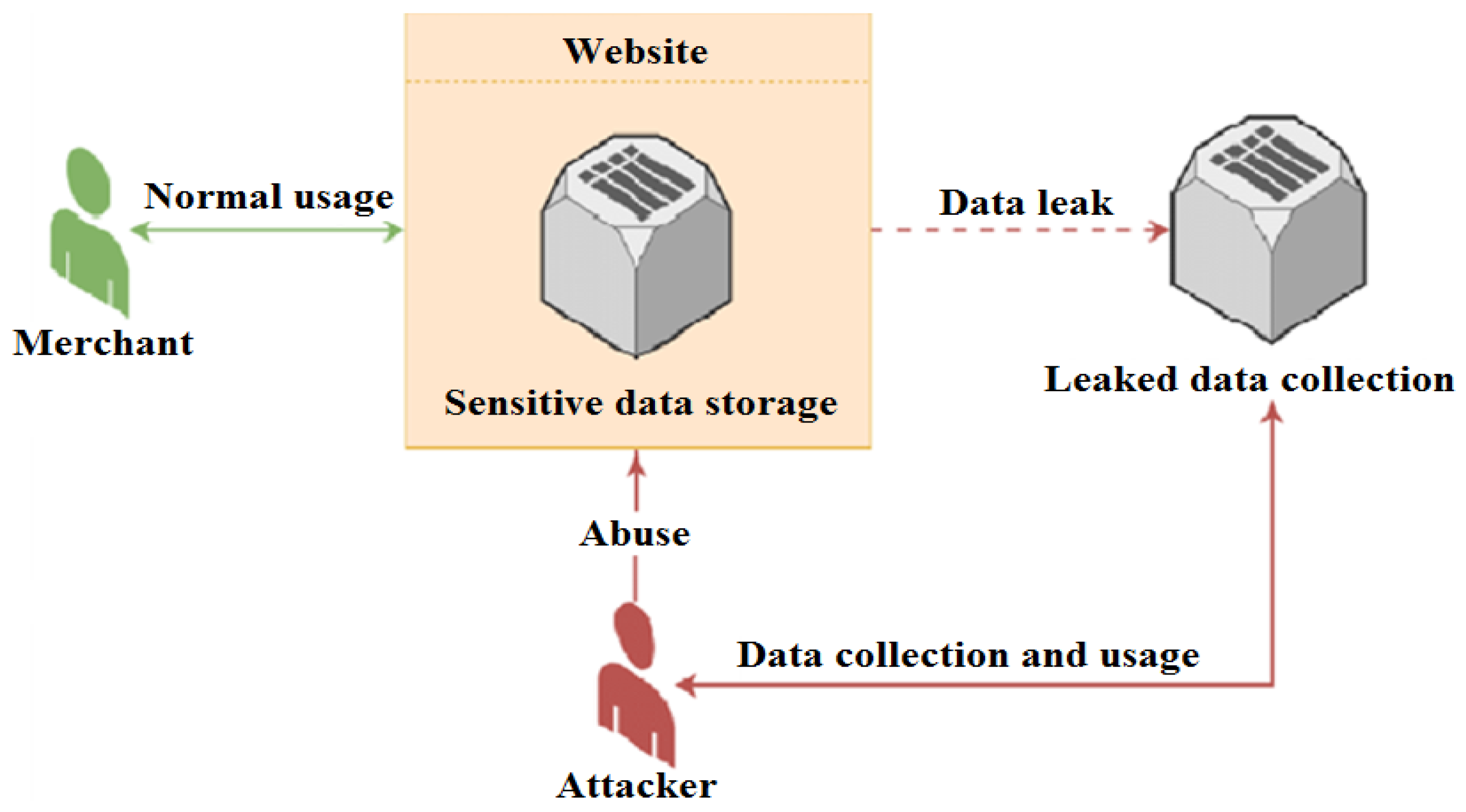
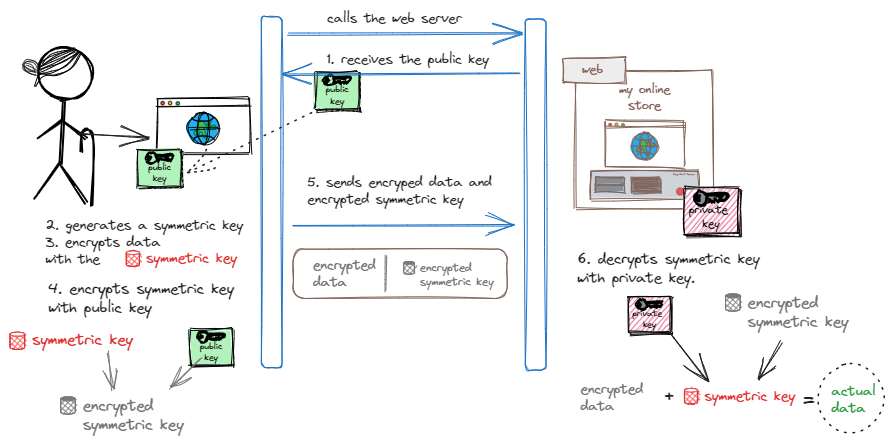
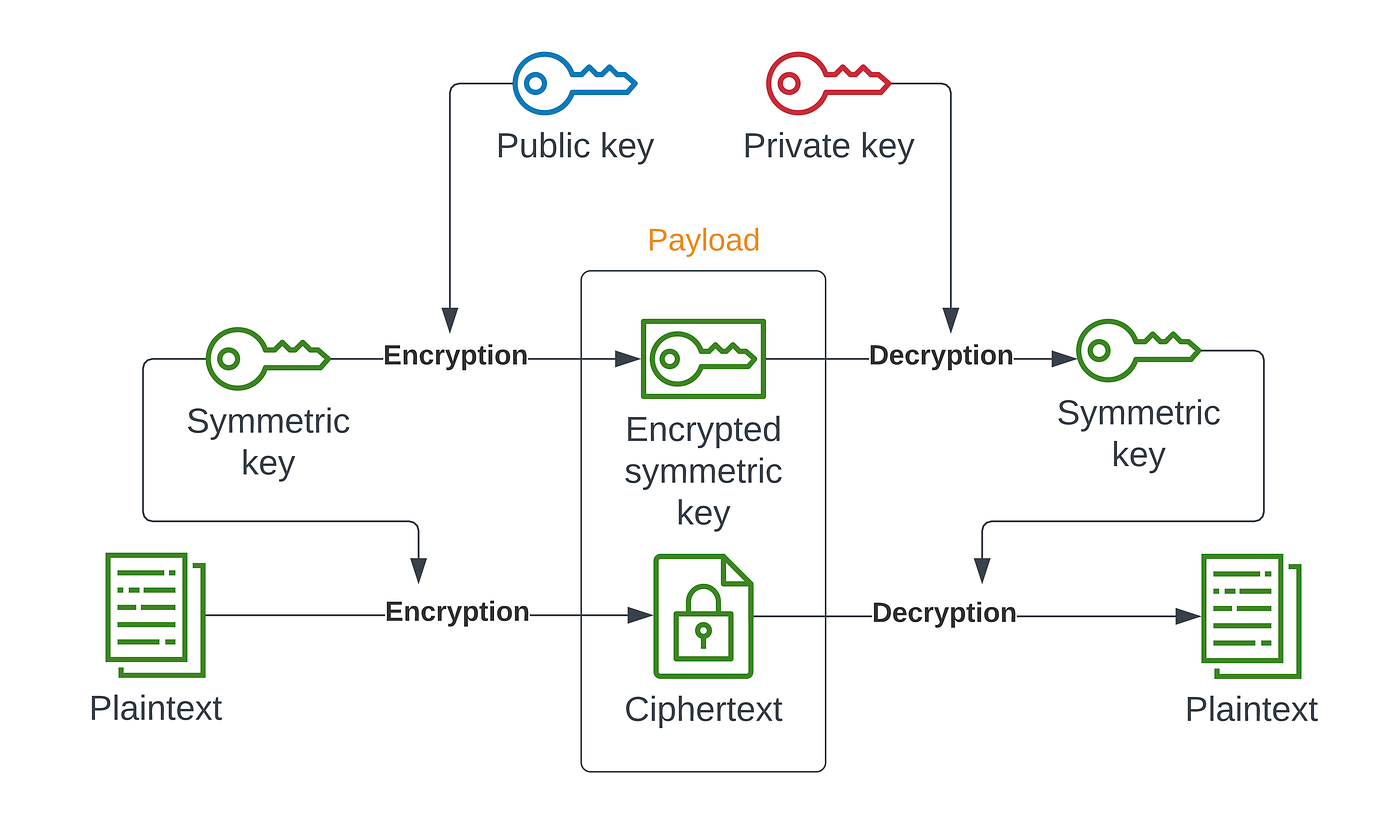
Future Internet | Free Full-Text | Applying Detection Leakage on Hybrid Cryptography to Secure Transaction Information in E-Commerce Apps